North Korea’s $1.5 Billion Crypto Theft: A Warning for Web3 Projects
Inside the Bybit Breach and What It Means for the Industry
This report was written by Tiger Research, analyzing North Korea's $1.5 billion cryptocurrency theft from Bybit, its sophisticated hacking strategies, and essential security measures for Web3 projects.
TL;DR
In February 2025, North Korean hackers stole cryptocurrency worth $1.5 billion from Bybit through social engineering attacks, part of an increasing trend of such incidents.
North Korea secures approximately 4-5% of its GDP through state-sponsored hacking operations, with tactics becoming increasingly sophisticated and refined.
Many Web3 projects lack proper security protocols. Projects should implement a tiered security approach: basic security (code reviews, education), intermediate measures (external audits, bug bounties), and advanced security (anomaly detection, dedicated teams).
1. Threats to the Blockchain Industry: Hacking
The blockchain market continues to experience numerous hacking incidents of varying scales. Among these, North Korea has emerged as a primary perpetrator in cryptocurrency-related cyberattacks. Operating professional hacking units at the state level, North Korea demonstrated its capabilities with the $1.5 billion breach of the Bybit exchange in early 2025.
These cyber operations serve multiple state objectives. They secure illicit funds used for regime operations and weapons development while also enabling the regime to bypass international economic sanctions. The frequency and sophistication of such attacks are expected to increase.
Given the rising threat posed by North Korea and other hacking groups, Web3 project leaders must recognize cybersecurity as a critical operational concern. This report analyzes North Korea’s hacking strategies and outlines practical, organization-level security measures to mitigate emerging risks.
2. The 2025 Bybit Hack
On February 26, 2025, the Federal Bureau of Investigation (FBI) announced that a North Korean hacking group was responsible for the theft of approximately $1.5 billion in cryptocurrency assets from Bybit.
2.1. The Bybit Hack in Three Phases
Phase 1: Initial Penetration – Developer-Level BreachAccording to Chainalysis, the attack began with a social engineering scheme. Hackers deceived a Safe{Wallet} (hereafter, Safe) developer by sending fraudulent emails or messages. When the developer interacted with malicious files or websites, the attackers gained access to the developer’s computer.
Safe and Mandiant later confirmed that this individual held elevated system privileges. Bybit relied on Safe, an external wallet provider, to safeguard customer assets. This arrangement was comparable to a bank outsourcing the security of its vault to an external security firm. The attackers targeted an employee who held a critical access credential within that firm. By compromising the employee’s computer, they bypassed the first layer of internal security, gaining entry into the vault’s broader control system.
Phase 2: Cloud Server Infiltration and Code ManipulationAfter gaining control of the developer’s computer, the attackers bypassed multi-factor authentication. This was equivalent to obtaining not only an access card from the security firm but also additional security codes. They stole access tokens for Amazon Web Services (AWS) and infiltrated the cloud server where Safe’s program code was stored—effectively the central control room of the vault system.
Once inside the control room, the attackers inserted sophisticated malware into Safe’s user interface code. This was similar to tampering with the monitoring system of a security company so that only one specific bank’s surveillance cameras showed manipulated footage. The malware specifically targeted Bybit wallets, making detection difficult. Other surveillance systems—equivalent to wallet services for other clients—continued to function normally, allowing both users and most security tools to overlook the breach.
Phase 3: Transaction Manipulation and Fund TheftAccording to Galaxy GK8 CTO Shahar Shamai, on February 21, the attackers altered a transaction parameter called Operation from the standard value '0' to '1'. This change triggered a function known as delegateCall, which enabled broader access rights. It was comparable to a bank employee believing they had approved a routine withdrawal, when in fact they had authorized permanent access to all of a customer’s accounts.
With this elevated permission, the attackers accessed Bybit’s cold wallets—offline storage systems—and transferred a substantial amount of cryptocurrency, including approximately 401,000 ETH, to their own addresses. Shamai noted that the change was subtle and difficult to detect through the standard transaction review interface. This was akin to bank employees seeing normal activity on their monitors and CCTV, while unauthorized withdrawals were taking place in real time.
Notably, Safe’s smart contract system remained technically intact. The vault and security systems were structurally sound, but the front-end interface was manipulated in a way that concealed the theft from internal monitoring. As a result, Bybit’s security team did not immediately identify any irregularities.
2.2. Bybit’s Response
As concerns spread, users began withdrawing funds en masse, creating a scenario comparable to a bank run. In response, Bybit CEO Ben Zhou issued a public statement assuring that the exchange remained solvent and that all customer assets were fully backed at a 1:1 ratio.
Within 72 hours, Bybit secured emergency funding from major industry players, including Galaxy Digital, FalconX, and Wintermute, to cover the losses. The exchange also launched a recovery bounty program, offering up to 10% of the recovered funds to individuals who assisted in retrieving the stolen assets.
Bybit’s rapid capital raise and transparent communication were key to stabilizing the platform and restoring user confidence. However, the incident highlighted a critical lesson for the broader cryptocurrency market: even large, well-resourced exchanges remain vulnerable to sophisticated cyberattacks.
3. Increasingly Sophisticated Hacking Strategies
North Korean cyber units apply a combination of social engineering and technical exploits to infiltrate blockchain-related systems—tactics broadly aligned with conventional hacking methods. They often impersonate recruiters or developers to deceive targets into downloading malware or accessing compromised links. Once installed, the malware grants attackers control over the system and access to sensitive data.
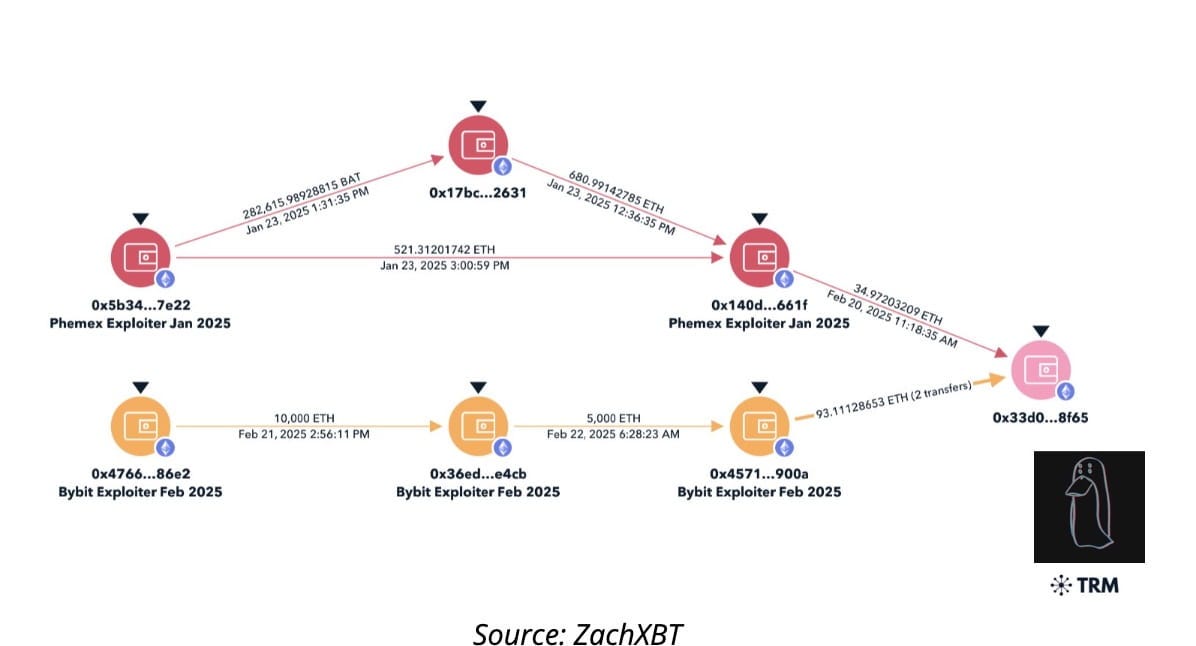
The key distinction between blockchain-based and traditional cyberattacks lies in the laundering of stolen funds. After extracting cryptocurrency, North Korean operatives initiate rapid and highly structured laundering processes designed to obscure asset traces. Stolen funds are divided into thousands of micro-transactions, moved across numerous intermediary wallets, and exchanged into multiple cryptocurrencies. A technique known as “chain-hopping”—which leverages decentralized exchanges (DEXs), cross-chain bridges, and mixing services in sequence—is frequently employed to complicate tracing.
Previously, groups such as Lazarus relied heavily on mixing protocols like Tornado Cash and Sinbad. As scrutiny and regulatory pressure on these services increased, their laundering methods evolved. The current strategy emphasizes speed and volume.
A notable tactic is the “flood-the-zone” approach, where assets are moved rapidly and in high volumes across multiple platforms. This overwhelms the tracking capabilities of investigators and regulatory bodies, making it difficult to follow fund flows and forcing the dispersion of investigative resources.
Eventually, most stolen assets are consolidated into Bitcoin and stored in wallets under the hackers’ control. These holdings are then laundered further through over-the-counter (OTC) brokers or exchanges with limited regulatory oversight. North Korea’s approach—combining advanced infiltration with agile laundering—continues to outpace the cybersecurity infrastructure of the blockchain industry.
4. Cyber Threats to Web3 Projects and the Importance of Security
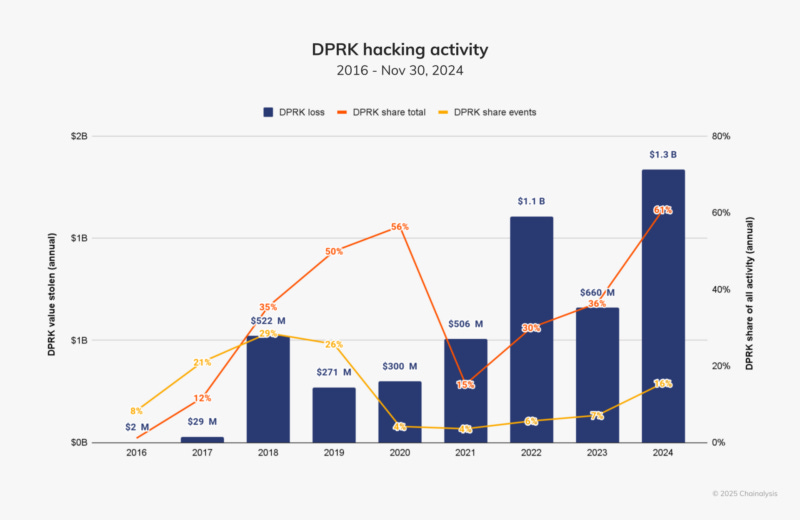
Cryptocurrency theft has become a core component of North Korea’s economic strategy. In 2023, the regime stole approximately $660 million in digital assets. This figure more than doubled in 2024, reaching an estimated $1.34 billion—equivalent to 4–5% of North Korea’s GDP. The Bybit hack in early 2025 alone accounted for more than 5% of its GDP, highlighting the extent to which cyber theft contributes to the regime’s financial operations.
Given the significant economic returns, North Korea is expected to continue expanding these activities. Other cybercriminal groups are also likely to pursue similar attacks, drawn by the high profitability of targeting the Web3 ecosystem.
4.1. Security Vulnerabilities in Web3 Projects
Despite the scale of emerging threats, many Web3 projects remain fundamentally unprepared to defend against sophisticated attacks. Unlike traditional companies that provide structured onboarding programs covering phishing prevention, device security, and data protection, onboarding in Web3 environments is often informal—conducted through Notion documents or Telegram chats. As a result, team members frequently lack not only essential security tools but also awareness of what is missing.
Most crypto projects are managed by small teams operating under tight launch timelines. In such environments, security is often viewed not as a foundational requirement but as a barrier to development speed.
A more critical challenge in Web3 lies in the irreversibility of trust breaches. Transactions signed on-chain cannot be reversed, and mechanisms common in traditional finance—such as fraud reporting or chargebacks—do not exist. As seen in the Bybit case, security incidents rarely remain isolated; a single breach can trigger broader market disruptions. This reinforces the need for heightened vigilance across the entire ecosystem.
4.2. Basic Security Strategies to Maintain in the Web3 Industry
Low-difficulty items—such as code reviews, account security, and basic security education—can be implemented immediately, regardless of team size or budget. These fundamental measures significantly reduce risk and serve as the foundation for building a sustainable security culture.
As projects grow and experience increased wallet connections or transaction volumes, it becomes practical to introduce medium-difficulty security practices. These include third-party audits, bug bounty programs, and log collection systems. Such measures strike a balance between addressing growing security demands and managing operational costs.
When a project’s managed assets surpass a critical threshold, high-difficulty security measures become essential. On-chain anomaly detection systems, dedicated security teams, and cyber insurance may appear excessive in early stages, but at scale, they are key to determining a project’s ability to respond effectively during security incidents.
When assessing security measures by level of difficulty, it is important to recognize that social engineering attacks—not just technical vulnerabilities—pose major threats in the Web3 environment. Recent blockchain hacking cases show a rising number of incidents involving phishing, identity theft, and privilege abuse, rather than direct smart contract exploits.
To mitigate these threats, technical defenses alone are not sufficient. In addition to ensuring the integrity of smart contract code, projects should implement security awareness training for team members and users, phishing response drills, and multi-factor authentication systems. High-difficulty measures such as anomaly detection and dedicated security teams should be designed with social engineering threats in mind, not just technical risks.
Decentralized projects that neglect security may be exposed to greater risk than centralized systems. This is due to the inherently wider attack surface in decentralized environments and the limited options available to reverse successful attacks. To establish a trusted security framework for investors and partners, technical controls must be supported by continuous training and management of human factors. Only a comprehensive approach can ensure both resilience and long-term growth for blockchain projects.
🐯 More from Tiger Research
Read more reports related to this research.Disclaimer
This report has been prepared based on materials believed to be reliable. However, we do not expressly or impliedly warrant the accuracy, completeness, and suitability of the information. We disclaim any liability for any losses arising from the use of this report or its contents. The conclusions and recommendations in this report are based on information available at the time of preparation and are subject to change without notice. All projects, estimates, forecasts, objectives, opinions, and views expressed in this report are subject to change without notice and may differ from or be contrary to the opinions of others or other organizations.
This document is for informational purposes only and should not be considered legal, business, investment, or tax advice. Any references to securities or digital assets are for illustrative purposes only and do not constitute an investment recommendation or an offer to provide investment advisory services. This material is not directed at investors or potential investors.
Terms of Usage
Tiger Research allows the fair use of its reports. ‘Fair use’ is a principle that broadly permits the use of specific content for public interest purposes, as long as it doesn't harm the commercial value of the material. If the use aligns with the purpose of fair use, the reports can be utilized without prior permission. However, when citing Tiger Research's reports, it is mandatory to 1) clearly state 'Tiger Research' as the source, 2) include the Tiger Research logo. If the material is to be restructured and published, separate negotiations are required. Unauthorized use of the reports may result in legal action.