Hacks recur across Web3 exchanges and projects every year. Unlike traditional firms, Web3 projects often collapse after a single breach. How should the industry respond?
Key Takeaways
As of April 2026, Web3 hacks are occurring in rapid succession, with 12 incidents reported in April alone.
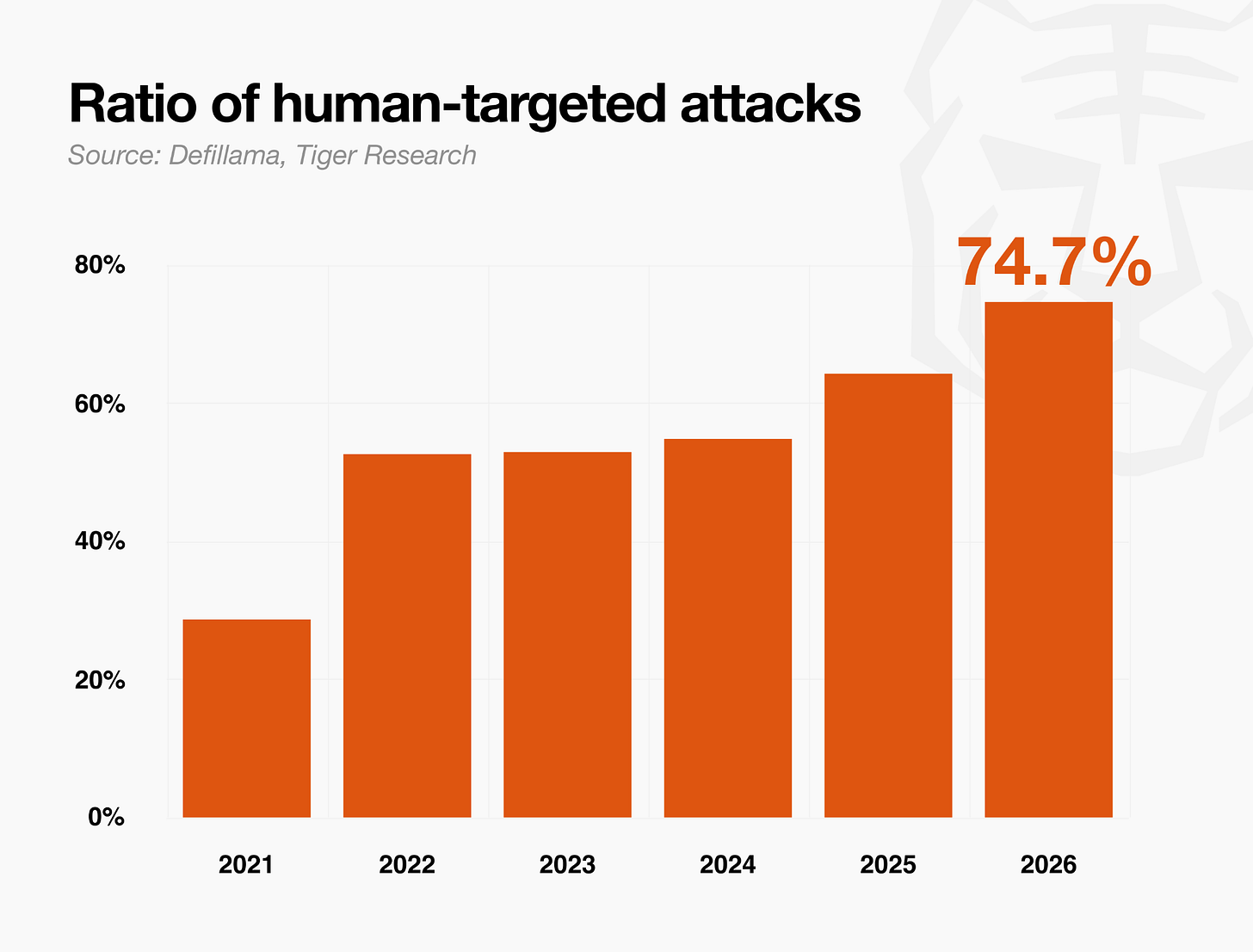
Social engineering’s share has grown every year, reaching 74.7% of total hack losses in Q1 2026. People are an easier attack vector than code.
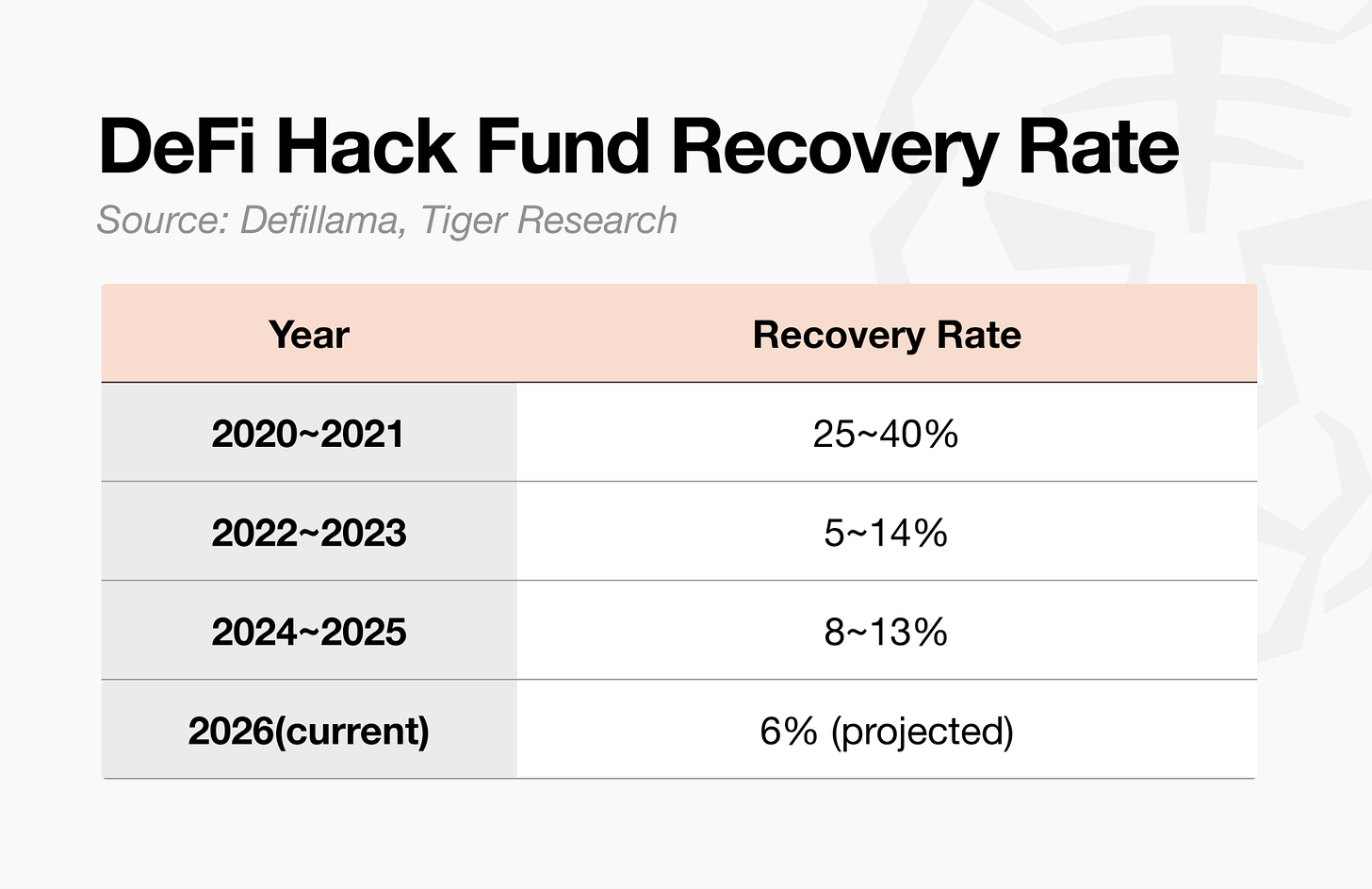
Since 2020, the average recovery rate for stolen funds has stayed below 10%. Unlike traditional finance, Web3 allows direct on-chain theft, so funds exit the moment a breach occurs.
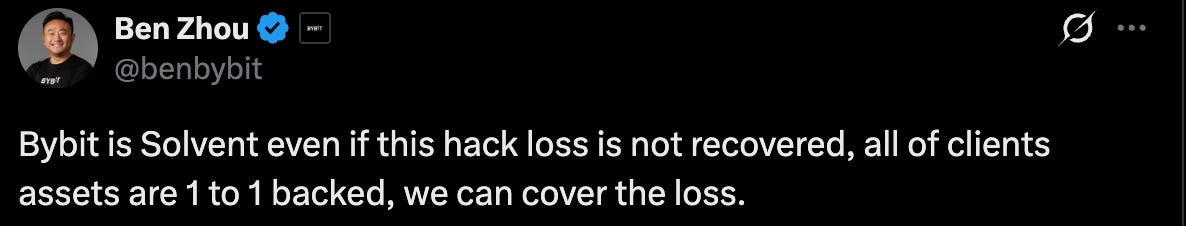
Bybit sustained a $1.5B hack but continued operations without investor losses, backed by exchange coordination and reserve funds. DeFi projects have no such option once assets leave the protocol.
Repeated hacks and sub-10% recovery rates are the decisive barrier keeping institutions out. Web3 needs structure and accountable operations, not philosophy.
1. Hacks Keep Happening
Hyperbridge, a bridge protocol connecting Polkadot and Ethereum, was exploited.
A flaw in the proof verification logic allowed the attacker to pass a forged cross-chain message, leading to the unauthorized minting of roughly 1 billion bridged DOT on Ethereum. Confirmed user losses stand at $2.5M across Ethereum, Arbitrum, Base, and BNB Chain.
Before the Polkadot bridge hack, DeFi protocol Drift Protocol suffered a $295.7M breach. A North Korea-linked group spent six months building trust with team members before seizing governance privileges, a highly refined social engineering operation. Tether later proposed a $127.5M support package, but the total aid of $147.5M fell short of covering the full $295.7M loss.
The hacks have continued since. Including smaller incidents after Drift, April alone saw 12 cases. As breaches pile up in an industry built on programmable finance, both investors and institutions are growing uneasy.
2. The Hacks Target People
The Drift Protocol hack originated from the compromise of a team member’s computer. The target was not a smart contract flaw or a system vulnerability, but a person.
The larger problem is that social engineering is taking up a growing share of Web3 hacks.
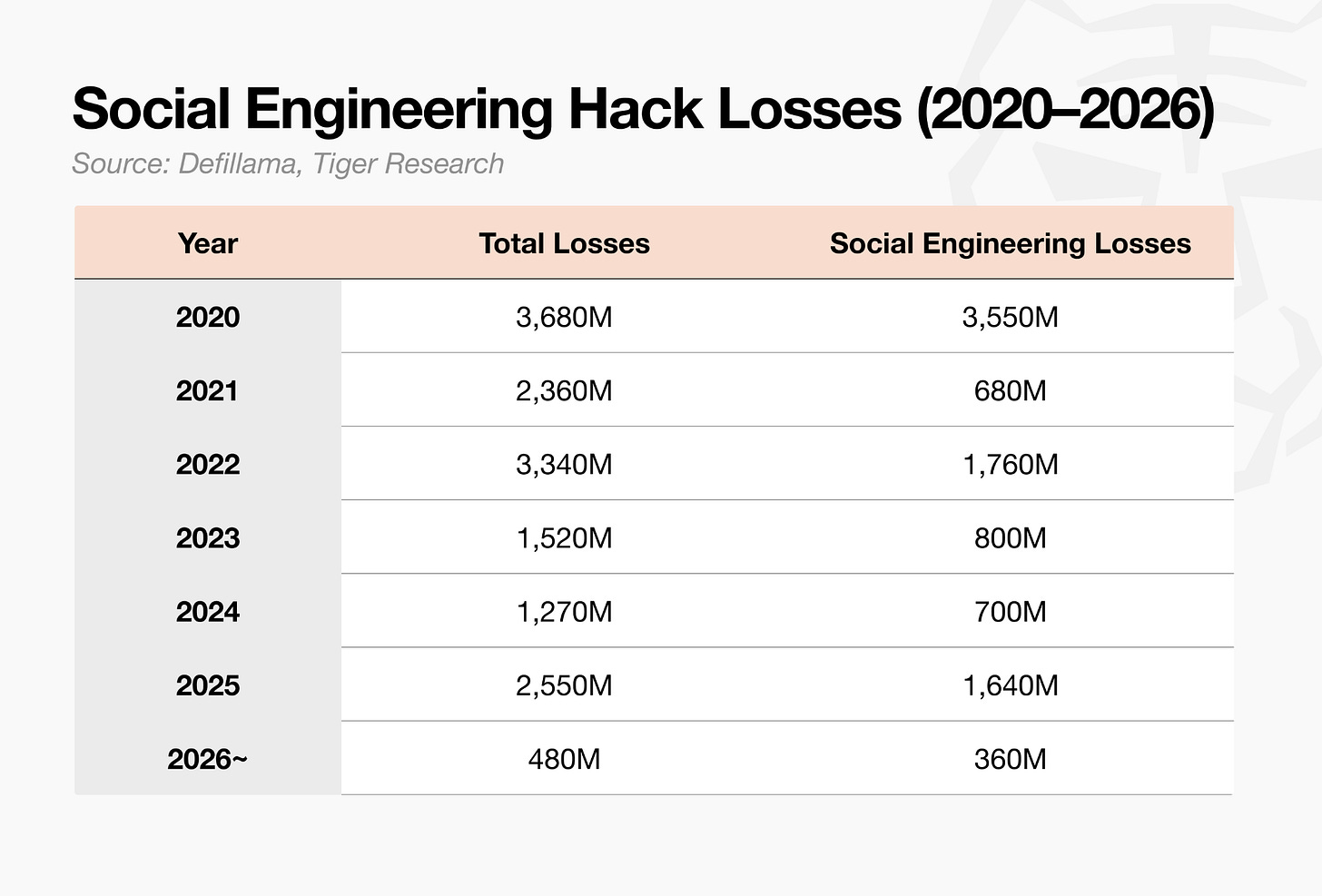
Social engineering accounted for 28.7% of total hack losses in 2021, rising to 64.3% in 2025 and 74.7% in Q1 2026. Attacks targeting people continue to expand, while code-level exploits have declined in relative share over the same period.
Given the open-source nature of blockchain, one might expect code-level exploits to dominate. In reality, social engineering has become the more prevalent attack vector. The reason is simple: compromising a person with existing privileges is easier than finding a flaw in the code.
Traditional industries show the same pattern. In 2025, 70% of corporate hacks involved social engineering. The playbook has carried over directly into Web3.
Web3, however, differs in one critical respect. In traditional finance, a successful breach rarely leads to outright theft. Account freezes, transfer reversals, and institutional intervention all apply. In Web3, protocol funds can be drained directly on-chain, and once a transaction is confirmed, there is no way to undo it.
That is what makes Web3 such an attractive target.
3. Falling Recovery Rates, Irreversible Losses
DeFi protocol hacks cause multi-billion-dollar losses each year, yet the share of stolen funds actually returned continues to fall. With state-backed operators like North Korea’s Lazarus Group and increasingly sophisticated laundering through mixers and cross-chain bridges, recovery has grown steadily harder.
If stolen funds could be returned, a minimum standard of safety would at least be preserved. But DeFi recovery rates remain stuck at low levels.
Average annual recovery has sat below 10% since 2020. The one outlier was the 2021 Poly Network hack of $611M, where the attacker voluntarily returned the full amount and pushed that year’s figure sharply higher. Excluding that event, every year has shown low recovery.
4. The Survivors Are Players With Agency
Not every Web3 player collapses after a hack. Unlike DeFi projects, which tend to fall apart after a single breach, some have managed to weather the damage.
In 2025, Bybit survived a $1.5B hack. Cross-exchange coordination and reserve funds sufficient to cover the loss made the difference. Not all stolen funds were recovered, but the exchange continued operating without investor losses, which is the key point. Exchanges broadly maintain separate SAFU funds to prepare for breaches and other contingencies.
DeFi projects have no such option. The moment a transaction goes through, protocol assets are gone, leaving no room to respond. The most realistic path to recovery is negotiation with the attacker, but attackers have little incentive to engage. With state-sponsored groups like Lazarus, negotiation is off the table entirely.
Traditional finance brings institutions in after a breach. Account freezes, investigations, insurance, and legal claims follow in sequence. Web3 has no authority capable of reversing a transaction. Projects have occasionally requested chain-level intervention to freeze assets, but a freeze is not the same as a return.
The core constraint remains. When something goes wrong in Web3, it cannot be undone.
5. Convincing Institutions in the Institutional Era
We live in the institutional era. Whether one accepts it or not, institutions are driving the market’s direction, and that current is not reversing.
If hacks continue and projects keep collapsing, there will be nothing to offer institutions. Institutional interest in blockchain and DeFi is already high. Operational efficiency in asset management, new yield structures, and a 24/7 market all make the space attractive.
But the case disappears if projects keep getting hacked and breaking down. No matter how compelling the efficiency gains or yield structures, the underlying assets must be safe. Recovery rates below 10% remain one of the largest reasons institutions stay on the sidelines.
Once institutional capital enters, the market scales beyond current comparisons. What unlocks that door is not technical superiority, but a trustworthy response framework. Whether the industry can defend decentralization while convincing institutions will determine whether Web3 advances to its next stage.
What Web3 needs now is not philosophy, but structure built for failure and operations built on accountability.
🐯 More from Tiger Research
Read more reports related to this research.Disclaimer
This report has been prepared based on materials believed to be reliable. However, we do not expressly or impliedly warrant the accuracy, completeness, and suitability of the information. We disclaim any liability for any losses arising from the use of this report or its contents. The conclusions and recommendations in this report are based on information available at the time of preparation and are subject to change without notice. All projects, estimates, forecasts, objectives, opinions, and views expressed in this report are subject to change without notice and may differ from or be contrary to the opinions of others or other organizations.
This document is for informational purposes only and should not be considered legal, business, investment, or tax advice. Any references to securities or digital assets are for illustrative purposes only and do not constitute an investment recommendation or an offer to provide investment advisory services. This material is not directed at investors or potential investors.
Terms of Usage
Tiger Research allows the fair use of its reports. ‘Fair use’ is a principle that broadly permits the use of specific content for public interest purposes, as long as it doesn’t harm the commercial value of the material. If the use aligns with the purpose of fair use, the reports can be utilized without prior permission. However, when citing Tiger Research’s reports, it is mandatory to 1) clearly state ‘Tiger Research’ as the source, 2) include the Tiger Research logo. If the material is to be restructured and published, separate negotiations are required. Unauthorized use of the reports may result in legal action.